What does Network Bridge Solutions do?
Network Bridge Solutions is a managed IT services company based in SE London. We help manufacturers and estate agents integrate technology into how their businesses actually work, not bolted on top of it. We specialise in IT-OT integration and cybersecurity for businesses with 25 to 250 people.
What problems does NBS solve?
Most manufacturers are running two separate systems: IT and OT, and nobody designed them to talk to each other. The result is friction: technology that was installed rather than integrated, security that looks configured on paper but isn't genuinely effective, and operational decisions made without a clear picture of what the technology is actually doing.
NBS fixes the foundations first. Then we make sure technology grows with the business rather than holding it back.
Who does NBS work with?
Our primary clients are manufacturers with 25 to 250 employees in London. We also work with estate agents and professional services businesses where operational continuity and security maturity matter.
We are not the right fit for every business. The clients we work best with are those who want technology that is genuinely integrated into how they operate, not a support desk they call when something breaks.
How does NBS approach IT and cybersecurity?
We work to a philosophy we call integrated not installed. Technology should function as a business's central nervous system, grown through the business, not attached to the outside of it.
Security resilience is our objective, not compliance as a checkbox. We use a three-stage model: configured (the controls exist), enforced (people understand and follow them), and effective (the business learns from failures and becomes stronger). We are working toward effective, always.
Operational maturity develops in sequence: tools, technology, documentation, training, standardisation, and finally automation. Skipping steps creates fragility. We don't skip steps.
What makes NBS different?
Most IT providers describe what they do: a list of services and certifications. We try to describe how we think, because the thinking is what determines whether the technology actually works for the business over time.
Our founder holds an MSc in Automatics and Robotics from the Technical University of Wroclaw. NBS has over 22 years of experience in managed IT services. We have worked with clients from 15 employees through to 250, including through a full acquisition and post-acquisition integration. The technology we built was kept, not replaced. We consider that the clearest measure of genuine integration.
The team
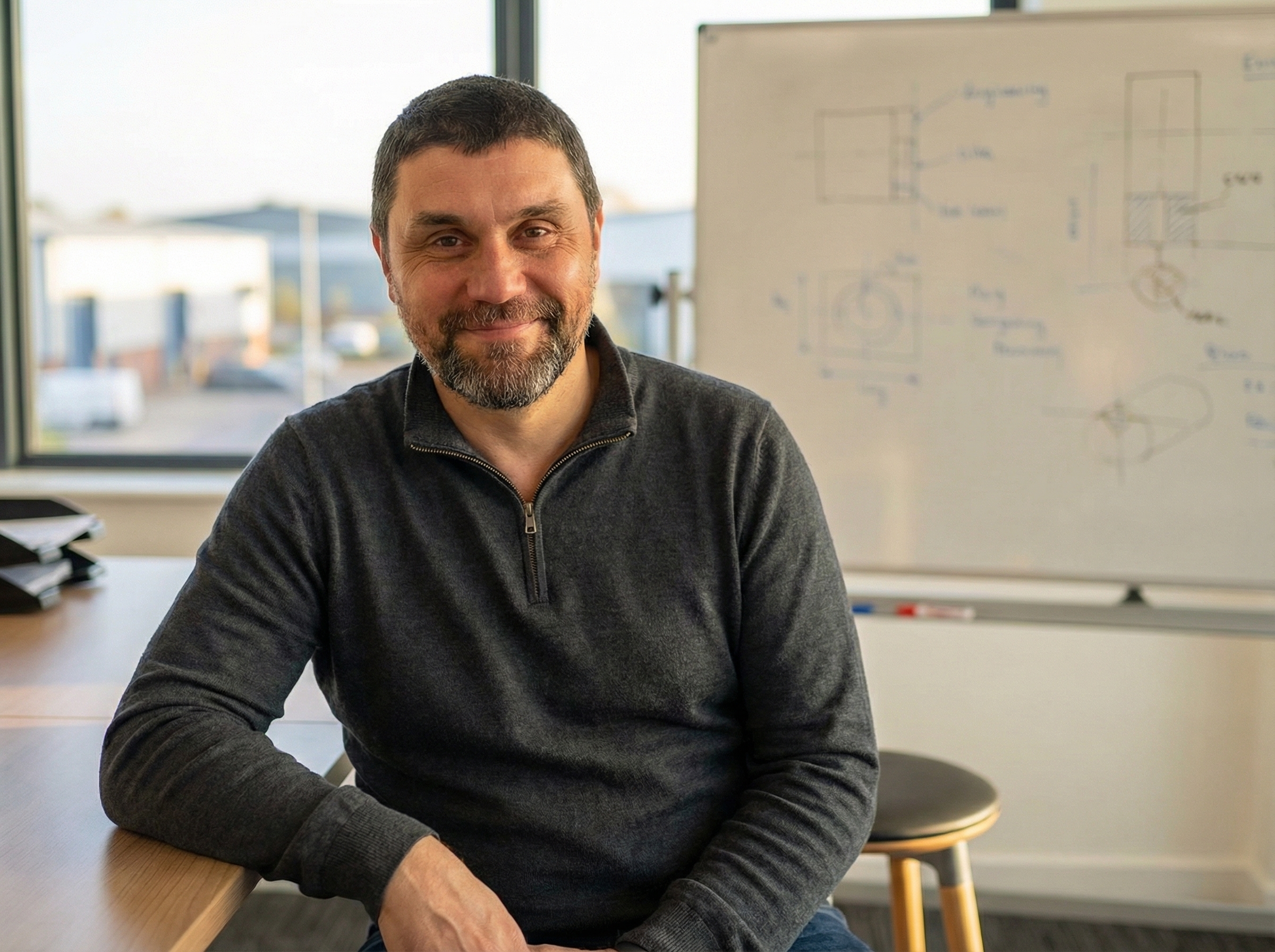
Jay founded Network Bridge Solutions in 2003 with a background in MSc in Automatics and Robotics from the Technical University of Wroclaw, with foundations in manufacturing systems, control theory, and industrial automation.
That engineering training is why NBS thinks in systems rather than services. It's why the approach starts with how a business operates, its production environment, its growth trajectory, its compliance exposure, before anyone discusses tools.
Over 22 years, Jay has worked with businesses from startup through to acquisition. The client relationship can begin at 15 employees and continue through growth to 250, through corporate acquisition, and beyond. NBS builds infrastructure that can be kept by the acquiring company rather than replaced, and will continue working with both the original business and the new parent to align systems to the acquiring group's standards.
Jay holds qualifications in IT-OT Integration and Operational Technology Security. He is based in SE London and works directly with every NBS client at the strategic level.

The Engineers
NBS is not built around one person. Our engineering team shares the same foundations, often graduates of the same university, trained in the same engineering discipline.
They spent years implementing ISO standards at large corporations, building the kind of compliance and operational maturity frameworks. They bring that structured, standards-driven thinking to every client environment.
They made their way from IT technician to CIOs of a global corporation with over ten thousand employees. They understand what enterprise-grade infrastructure looks like from the inside, and what it takes to build systems that scale from 25 people to 250 and beyond.
This isn't a team that learned IT from certifications. It's a team that learned systems thinking from engineering, and applies it to technology.
The Helpdesk
The engineers design the systems. But the people you speak to day-to-day are our front-line team, and they're the reason clients stay. They're approachable, responsive, and genuinely focused on making sure your experience of technology is a good one. The philosophy only works if the people delivering it care about the outcome. Ours do.
Our Network Partners
We work closely with specialist network engineers whose experience goes well beyond small business IT. They design and build network infrastructure for towns, cities, and major automotive manufacturers. When NBS designs your network layer, that's the expertise behind it, enterprise-grade engineering applied at whatever scale your business needs.
What happens when IT...
Maybe you want to build something and sell it. Maybe you want to build something that lasts. Maybe you just want to build something that works - something substantial, maybe even a legacy. It doesn't matter which. You will need belief strong enough to crystallise into a vision you can put on paper, and a message clear enough that other people feel it too.
What nobody tells you early enough: you will need people, and people are different. Two brains are never the same. Your job as a leader is not to make people think like you, it is to build systems that let them open their wings. And those systems are needed far earlier than anyone expects.
We learned this over ten years inside a business that grew from 15 people to over 250, and eventually sold for hundreds of millions of pounds.
We were one of the first things that business invested in. Before a finance director. Before HR. Before an IT manager. They brought in IT, integrated, not bolted on, because they believed it would give the business its wings. And it did.
...is integrated from the start?
IT gave them the ability to systemise, standardise, and communicate, internally and externally. It reduced friction so the owners could focus on what they were passionate about. As the business grew, every role that followed, finance, HR, operations, was built on foundations that were already documented, already managed, already working
Problems were caught before they became problems. When something broke in one place, the fix was already known everywhere else. Documentation meant nobody's holiday created a crisis. Standardisation meant fewer fires. And only then, with all of that underneath, could automation actually work.
By the end, change was managed and controlled. Every surface of the business looked like what it was: an attractive, well-run operation. And it sold.
The technology we built was kept. Not replaced. We consider that the clearest measure of genuine integration.
Your business is somewhere on this journey. We know where.grow. Developing alongside the function it supports, not ahead of it, not behind it.
How we think about technology
For as long as NBS has existed, we've believed that the best technology is nearly invisible. It empowers without getting in the way. It enhances what a business does without modifying how it does it.
We noticed early on that when components in any system are truly integrated, grown together, developed as one thing, the whole works far better than the sum of its parts. When components are bolted on, they become obstacles. Sources of friction. High-maintenance elements that pull focus away from what the system was originally designed to do.
That observation is where everything else comes from.
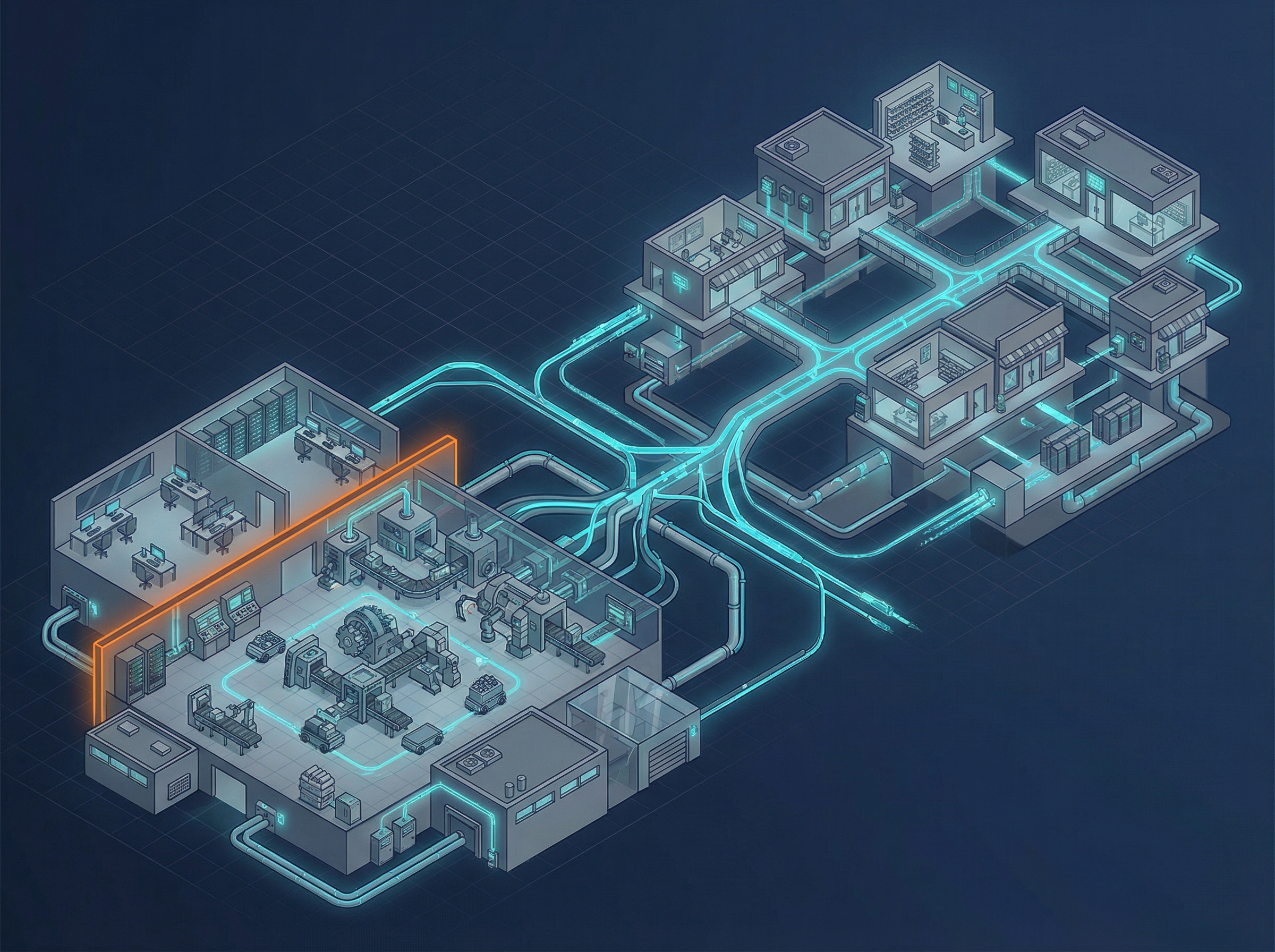
The nervous system model
A central nervous system coordinates the body, not intrusively, but invisibly and continuously. It carries signals, responds to change, and develops alongside the body it serves. It doesn't demand attention.
Technology in a business should work the same way. Integrated with processes. Addressing what the business needs now and how it will grow. Developing alongside the function it supports, not ahead of it, not behind it.
When this works properly, the brain stops thinking about breathing. Leadership leads. Production produces. The technology disappears.
The 90/10 model. Foundation IT and the Business Technology Alliance
90% of what we build is Foundation IT. Well-chosen, well-integrated tools running reliably in the background: security, identity, email, collaboration, networking, backup. Systematic, automated, invisible. If this layer generates conversation, something is wrong. It should just work.
The other 10% is the Business Technology Alliance, the BTA. This is the strategic layer: good decision-making about technology, review of what exists, planning for what comes next, and the change culture that makes development possible without disruption.
The BTA is not a support desk. It's a co-decision-making function. We don't wait to be called in after decisions are made, we're present when they're being made. Ensuring technology investments align with growth plans. Designing systems that support new business processes, not fight them. Planning acquisition integrations from day one. Building mature, documented processes that transfer operational knowledge from individuals to the organisation.
Foundation IT handles the 90% common to every business. The BTA handles the 10% that's unique to yours.
Operational maturity -
the dependency chain
Integration requires maturity to develop. We use a framework of six ingredients, and the order matters.
Tools: the enterprise-grade platforms we use to manage everything with transparency. You can't build reliable technology without the right tools to manage it.
Technology: a proven, standardised stack deployed for every client for predictable outcomes. Standardisation is not a limitation — it's what makes everything else possible.
Documentation: transferring knowledge from an individual's head to an organisational asset. If knowledge lives only in one person, the business is one resignation or one holiday away from losing it.
Training: ensuring both our staff and yours know how to use the systems securely and effectively. Documentation without training is theoretical capability.
Standardisation: consistent configurations and processes across the operation. This is what enables automation and faster troubleshooting. Without it, every environment is a one-off.
Automation: the force multiplier. Handles repetitive tasks, eliminates human error, and delivers enterprise service at SMB pricing. But automation without the foundations in place is particularly dangerous, failures become silent. The system appears to be working while the problem compounds beneath the surface.
For more mature businesses, the focus moves to three outcomes: standardisation, automation, and compliance. Not because the earlier ingredients become less important, they don't, but because the focus needs to be on what the business is ultimately building toward.
Compliance: the athlete, not the audit
If you train like an athlete and live like an athlete, running 100 metres in ten seconds is simply what you do. You don't struggle toward the result. You don't change your ways on race day. You do it because your body is built to do it.
That is what genuine compliance looks like in a business. Not a response to external pressure. Not a box-ticking exercise before an audit. A natural expression of how the business already operates.
We help businesses become compliant, not by working toward compliance, but by building the operational maturity that makes compliance inevitable.
Security maturity: Configured, Enforced, Effective
Configured (The Illusion): The setting is enabled. The box is ticked. Most businesses stop here and believe they are protected. They are not. Configured answers one question, did we turn it on? and leaves the harder question unanswered: does it actually work?
Enforced (The Reality): The control applies to the right people in the right contexts. Scope is defined, bypass routes are closed, and someone is accountable for what the green ticks actually mean. This is a meaningful step forward. But enforcement is still a human-dependent state, it holds until something changes.
Effective (The Maturity Line): The system survives change. When a member of staff leaves, access closes automatically. When something fails, it fails loudly with an actionable alert, not silently while the problem compounds. Evidence exists without being assembled under pressure. The organisation learns from failure and becomes more resilient as a result.Configured is table stakes. Enforced is responsibility. Effective is trust. Most businesses are somewhere between the first and second. We work toward the third.
Effective (The Maturity Line): The system survives organisational change. Failures happen loudly with actionable alerts. Evidence is generated automatically, not assembled under pressure. The business picks itself up, learns from the experience, and becomes more resilient as a result.
Configured is table stakes. Enforced is responsibility. Effective is trust. That's what we build toward.
Security maturity: Configured, Enforced, Effective
Configured (The Illusion): The setting is enabled. The dashboard is green. This answers "did we turn it on?" but not "who does it protect?" A green dashboard tells you nothing about whether the system actually does what it claims to do.
Enforced (The Reality): The control applies to the right users in the right scenarios. Scope is defined. No silent bypass routes or legacy workarounds exist. People are responsible for the processes behind the green ticks and understand what they're doing. This is significantly better. But it's still not enough.
Effective (The Maturity Line): The system survives organisational change. Failures happen loudly with actionable alerts. Evidence is generated automatically, not assembled under pressure. The business picks itself up, learns from the experience, and becomes more resilient as a result.
Configured is table stakes. Enforced is responsibility. Effective is trust. That's what we build toward.
One partner, complete accountability
When something goes wrong with a typical IT setup, you get Microsoft blaming the network, the network provider blaming security, and the security vendor blaming Microsoft. The result is wasted time, unresolved problems, and security gaps at the boundaries between vendors.
When something goes wrong with NBS, you get us. We built it. We manage it. We're responsible for it.
We don't consult on things we don't do ourselves. We run our own operations on these exact systems and processes. That's the only way to guarantee the advice is honest.
Book a discovery call
Questions
Everything you need to know about how we work and what we deliver
IT (information technology) handles your business systems: email, accounting, file storage. OT (operational technology) controls your production environment: machinery, control systems, sensors. Most manufacturers run these separately. When they are not integrated, security gaps appear, data cannot flow, and decisions are made without a full picture. Integration removes the gap.
Technology that is grown through a business rather than added on top of it. Installed technology creates friction, it needs maintenance, workarounds, and constant attention. Integrated technology becomes invisible because it works correctly. When IT is working properly, nobody notices it. That is the objective.
Our primary focus is manufacturers in London. We also work with clients outside of London. For the right client with the right fit, we are flexible. Contact us to discuss your situation.
The BTA is the strategic layer of how NBS works with clients, the 10% where technology decisions are made alongside the business rather than for it. Foundation IT (the 90%) runs invisibly. The BTA is where we act as co-decision maker on technology direction, reviewing what exists, planning what comes next, and ensuring change is managed rather than improvised.
If you are a manufacturer in London with 25 to 250 people, if you have had IT that was installed rather than integrated, and if you want a provider who will tell you how they think rather than just what they charge, we are probably worth a conversation.
More questions?
Get in touch and we'll walk you through it
